You spent weeks building a proposal. Your stack is impressive — next-gen SIEM, EDR, zero trust architecture, cloud-native monitoring, threat intelligence feeds. You listed every tool, every integration, every certification badge you hold. You hit submit with confidence.
Then you lose to a competitor with half the tech stack.
It happens constantly. And if you’re regularly losing cybersecurity RFPs despite having strong technical capabilities, the problem probably isn’t your tools. It’s how you’re presenting them.
The Core Problem with Tool-Heavy Proposals
When evaluators open a cybersecurity proposal, they aren’t reading it the way a fellow security engineer would. Modern RFP review committees include procurement officers, legal counsel, compliance leads, finance stakeholders, and executives — not just IT managers. Each of them is reading your document through a completely different lens.
Cybersecurity questions in RFPs are rarely about whether you use a specific product. They are about how risk is identified, handled, and owned. Many responses fail because they read like a list of tools rather than an explanation of how security decisions are made and enforced. Reviewers look for evidence that controls operate within a broader risk management approach, not in isolation.
A proposal that leads with tool names signals vendor thinking, not client thinking. It tells evaluators that you’re selling what you have — not solving what they need.
What Evaluators Are Actually Scoring
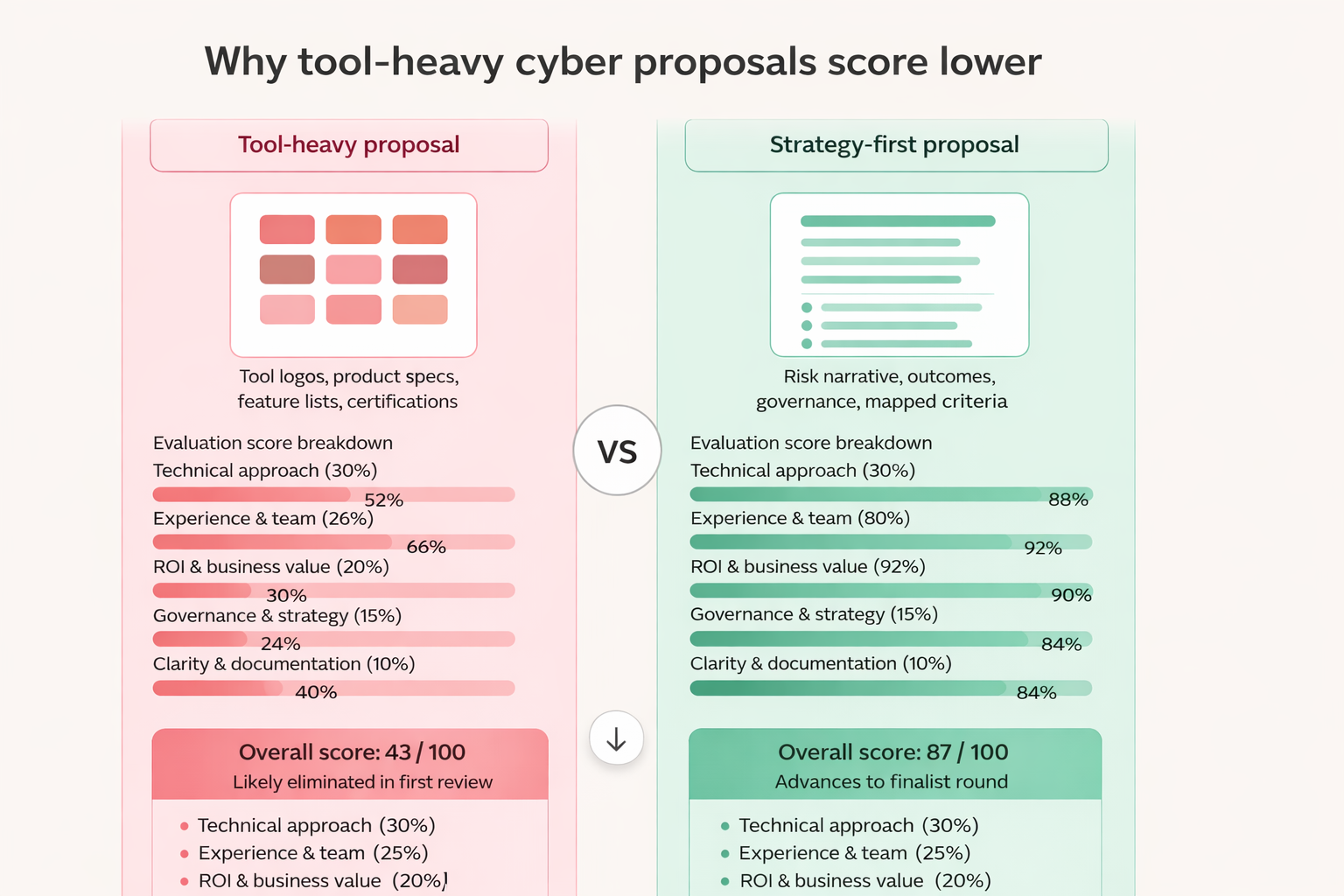
Understanding the scoring rubric is everything. Most cybersecurity RFP evaluation frameworks weight criteria across several dimensions — and technical tools are rarely at the top.
Proposals are commonly evaluated on technical approach (30%), experience (25%), cost (20%), reporting and documentation quality (15%), and timeline (10%).
Notice what’s missing from that breakdown: a line item for “number of tools deployed” or “size of tech stack.” Technical approach is scored — but it’s approach that matters, not tooling. A proposal that explains how you think about a client’s threat environment scores higher than one that lists every product in your portfolio.
Functionality, security, and vendor expertise often outweigh cost in proposal scoring. Scalability and innovation — how well a vendor can grow with the business and bring fresh ideas — frequently earn extra credit.
Evaluators are looking for a strategic partner. They want confidence that you understand their risk posture, their regulatory landscape, and their operational constraints. A wall of product logos doesn’t give them that confidence.
Five Reasons Tool-Heavy Proposals Lose Points
1. They Lack Coherence Across Sections
One of the most common technical reasons tool-centric proposals fail is internal inconsistency. Cybersecurity RFPs are structured to test the same claims repeatedly across different sections. Responses fail when the access control model described in one section contradicts the identity workflow described in the security questionnaire. The security story must remain coherent as it moves from technical controls to operations to legal commitments.
When a proposal is organized around tools rather than a unified security narrative, contradictions emerge. The EDR section doesn’t connect to the incident response section. The compliance documentation doesn’t reference the threat monitoring workflow. Evaluators notice — and deduct points.
2. They Don’t Demonstrate Understanding of the Client’s Risk
A well-crafted cybersecurity RFP is about finding a strategic partner, not just a vendor. The RFP outlines the threat, and the response must detail the defense.
A tool-heavy proposal typically describes what your solution does in general terms — not what it will do for this specific client against their specific risks. Evaluators want to see that you’ve read their threat environment, understood their regulatory requirements, and mapped your approach accordingly.
3. They Signal Integration Risk
The more tools you list, the more integration complexity you imply. Procurement teams have been burned before by vendors who sold a multi-tool solution that became a support nightmare. By 2030, many businesses are expected to work with fewer suppliers, bundling products or services, with the remaining vendors expected to meet rigid requirements for data security and operational simplicity.
Listing a dozen tools without explaining how they work together as a cohesive system is a red flag to experienced evaluators, not a selling point.
4. They Obscure ROI and Value
Buyers want clear ROI and long-term value. Lowest cost rarely wins — but neither does the most expensive stack without a clear value case.
Tool-heavy proposals tend to skip the business value conversation. They demonstrate capability but not impact. What does this architecture reduce in terms of breach risk? What compliance penalties does it help avoid? What does faster detection translate to in business continuity terms? These are the questions scoring panels ask — and tool lists don’t answer them.
5. They’re Harder to Evaluate Fairly
Evaluators score proposals against weighted criteria matrices. Too much detail overwhelms evaluators, while vague criteria create confusion. Clear, evidence-based responses strike the right balance and stand out more in review sessions.
A dense technical appendix packed with product specifications forces evaluators to do interpretive work. They have to figure out what your tools mean for their requirements. Proposals that map directly to stated criteria — and speak the language of the RFP — score higher simply because they’re easier to evaluate.
What High-Scoring Cyber Proposals Look Like
The vendors consistently winning cybersecurity RFPs are making a deliberate shift: from tool-centric to outcome-centric writing. Here’s what that looks like in practice.
Lead with risk, not technology. Open your technical section by demonstrating that you understand the client’s specific threat landscape, regulatory requirements (NIST, ISO 27001, GDPR, HIPAA), and operational constraints. Tools come later, as the means to an end.
Tell a coherent security story. Your proposal should read like a logical argument: here is the risk environment, here is our methodology for addressing it, here are the controls we implement, here is how we measure effectiveness, here is what happens when something goes wrong. Tools support that story — they don’t replace it.
Map to evaluation criteria explicitly. Vendors who align their answers with scoring rubrics highlight strengths in ways evaluators can measure, giving them an edge against vendors who treat the RFP as a generic questionnaire. Read the RFP’s scoring section carefully and structure your response around what’s being evaluated.
Quantify outcomes. Where possible, ground your technical capabilities in measurable outcomes. Faster mean time to detect (MTTD), reduced attack surface, compliance audit pass rates, incident response SLAs. Numbers speak to every member of the evaluation committee, regardless of technical background.
Address governance, not just tools. Organizations with procurement processes that explicitly evaluate regulatory compliance spend significantly less on remediation and penalties. Sophisticated evaluators want to understand your governance model: how decisions are made, how controls are monitored, how exceptions are handled. Mature governance signals mature security.
The Strategic Shift That Changes Outcomes
Winning cybersecurity proposals are built around a simple insight: the buyer isn’t purchasing a technology stack. They’re purchasing risk reduction, compliance confidence, and operational resilience.
Your tools are evidence for those claims — not the claims themselves.
When you restructure your proposal around what the client is actually trying to achieve, every tool you mention gains context and credibility. The SIEM isn’t just a SIEM — it’s how you detect anomalous credential use within minutes, which directly addresses the threat pattern described in their RFP.
That kind of proposal is harder to write. It requires you to internalize the client’s perspective rather than translate your own capabilities. But it’s the kind of proposal that scores well across every column in the evaluation matrix — technical, strategic, financial, and relational.
The next time you’re tempted to open with your tech stack, stop. Start with the threat. Build the story. Let the tools do their job: support the argument, not be the argument.
Looking to improve your cybersecurity proposal win rate? Focus on strategic alignment, coherent risk narratives, and outcomes-first writing — not feature lists.